When a company entrusts its IT infrastructure and networks with a data center, it wants to have an assurance that the very latest in physical security standards will be implemented. Some of these features are easy to evaluate. A data center should “look” secure, for instance, meaning it should be set back from busy highways (preferably obscured by trees or other barriers) and force all traffic to enter through a single gate. Once inside that outer perimeter, however, things get a little more complicated and, in some cases, less obvious.
What is Data Center Security?
Data center security refers broadly to the array of technologies and practices used to protect a facility’s physical infrastructure and network systems from external and internal threats. On a very basic level, data center security is all about restricting and managing access.
Only authorized personnel should be able to access critical infrastructure and IT systems. Data center security includes both the “things” put in place to accomplish that goal (such as locked access points, surveillance systems, or security personnel) and the “controls” that manage them (such as security policies, access lists, or rules for handling data).
How to Secure a Data Center
Today’s data centers are far more complex than a warehouse space filled with servers. They are often designed from the ground up with security best practices in mind. Every element of a data center’s physical security should be implemented with other elements in mind so that they form an interlocking network of security measures, each one enhancing the effectiveness of the others.
However, no amount of physical security will provide much protection without a holistic security policy to manage it all. Protocols and procedures for common and unusual contingencies need to be in place to provide data center personnel with clear guidelines for how data center operations should be carried out.
These controls need to be developed in advance and regularly tested to ensure that everyone knows how (and why) to keep the facility secure from potential threats.
By implementing a “Zero Trust” security philosophy, data centers can greatly reduce the risk of unauthorized access because everyone is subjected to the same high level of scrutiny and must verify their identity and reason for accessing assets at every turn. Like any other data center policy, these processes should be audited regularly to ensure their effectiveness.
Data Center Tiers and Security
While data center tiers don’t directly reflect security standards, higher tier facilities (Tier 3 or 4) are typically larger and more complex environments. As a result, they tend to incorporate more sophisticated and extensive security measures.
Higher tier data centers have more redundant infrastructure, all of which must be protected in order to ensure high levels of uptime reliability. In the case of enterprise-grade facilities, there are often more extensive compliance requirements that will necessitate more robust controls for managing access and data.
Important Data Center Security Standards
Here are a few critical data center physical security standards and technologies every colocation customer should evaluate when they’re looking to partner with a facility.
Layered Security Measures

Every aspect of a data center’s security should work in concert with other elements as part of a comprehensive, layered system. The idea is that a potential intruder should be forced to breach several layers of security before reaching valuable data or hardware assets in the server room. Should one layer prove ineffective, other layers will likely prevent the intrusion from compromising the entire system.
Access Lists
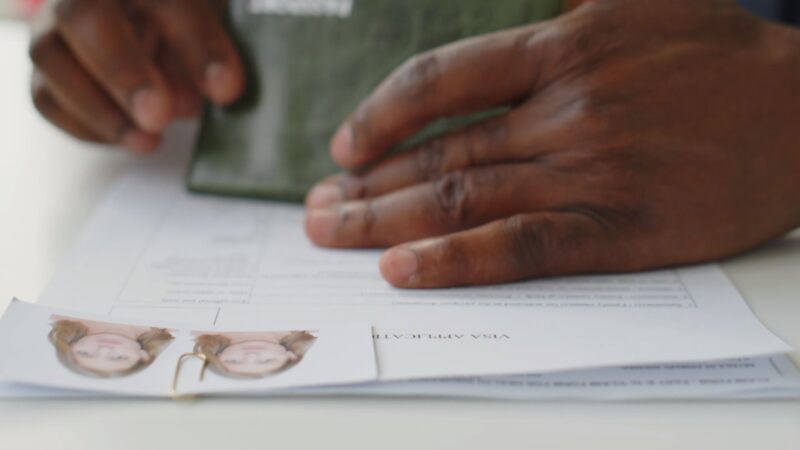
While it may seem like a simple thing, one of the most important elements of data center security is ensuring that only authorized persons are permitted to access key assets. When a company collocates with a data center, not every employee there needs to have access to the servers.
This is a critical component of the “Zero Trust” security philosophy. By maintaining up-to-date access lists, a facility can help their customers prevent theft and guard against human error by people who aren’t authorized to handle IT assets in the first place.
Video Surveillance

Another longtime staple of physical security technologies, video surveillance is still incredibly valuable for data centers. Closed-circuit television cameras (CCTVs) with full pan, tilt, and zoom features should monitor exterior access points and all interior doors as well as the data floor itself. Camera footage should be backed up digitally and archived offsite to guard against unauthorized tampering.
Secure Access Points
Sensitive zones like the data floor should be secured by more than a simple locked door. Manned checkpoints with floor-to-ceiling turnstiles or man-traps that prevent an authorized visitor from passing credential back to someone else are essential physical security standards for any data center facility.
24x7x365 Security

Security checkpoints, cameras, and alarms won’t amount to much without security staff on-site to respond to potential threats and unauthorized activity. Routine patrols throughout every data center zone can provide a visible reminder that security personnel are on the lookout and can react quickly to deal with any potential issue.
RFID Asset Management
While having data center security personnel on-site and archived camera footage available is critical, it’s still difficult to keep eyes on every piece of hardware at all times. With RFID tagging, data centers can manage and track assets in real-time through powerful business intelligence software. Tags can even send out alerts the moment an asset is moved or tampered with, allowing data center personnel to respond quickly to any threat.
Background Checks
Between security staff and remote hands technicians, data centers have a lot of people moving throughout a secure facility. Conducting thorough background checks on staff, as well as implementing vetting requirements for all third-party contractors, can provide assurances to their customers that these people can be trusted to manage and protect their valuable IT assets.
Exit Procedures
When someone who has the authorization to access sensitive zones and assets within the data center leaves their position, their privileges don’t go with them. Whether it’s data center personnel or customer employees with access rights who are leaving the organization, facilities should have systems and procedures in place to remove those privileges. This could mean updating access lists, collecting keys, or deleting biometric data from the facility’s system to make sure they won’t be able to pass through security in the future.
Multi-Factor Authentication
Every data center should follow “Zero Trust” logical security procedures that incorporate multi-factor authentication. Every access point should require two or more forms of identification or authorization to ensure that no one will simply be “waved through” by security if they’re missing one form of authentication.
Biometric Technology

One of the latest innovations in security standards, biometric technology identifies people through a unique physical characteristic, such as a thumbprint, retina shape, or voice pattern. There are a variety of ways to incorporate biometric technology into access protocols, and it is especially valuable as one component of two-factor authentication.
As data center security technology continues to involve, new physical security measures will surely be incorporated as best practices. Data center physical security standards may not be evident at first glance because many of them are intended to remain out of sight. Even so, data center customers can review security certifications and request a more detailed overview of the physical and logical security measures a facility has put in place to ensure that data remains well-protected.
FAQs
What is the difference between physical and logical data center security?
Physical security pertains to the tangible measures in place to protect the facility, such as surveillance cameras, access controls, and security personnel. Logical security, on the other hand, refers to the digital measures, like firewalls, encryption, and intrusion detection systems, that protect data and network systems.
How often should data center security measures be reviewed and updated?
Ideally, data center security measures should be reviewed at least annually. However, with the rapid evolution of technology and emerging threats, it’s beneficial to conduct periodic assessments and updates more frequently.
Are there international standards for data center security?
Yes, there are several international standards, such as ISO/IEC 27001, which provides guidelines for information security management systems.
How do data centers handle natural disasters or unforeseen events?
Many data centers have disaster recovery and business continuity plans in place. This includes backup power sources, data redundancy, and off-site backup facilities to ensure data integrity and availability during unforeseen events.
What role does encryption play in data center security?
Encryption is a crucial logical security measure. It ensures that even if data is accessed or intercepted, it remains unreadable without the appropriate decryption key.
Final Words
Data center security is a multifaceted domain that requires a harmonious blend of physical and logical measures. As technology evolves and threats become more sophisticated, the need for robust and adaptive security measures becomes paramount. By understanding and implementing the latest security standards and best practices, data centers can ensure that they offer a safe and reliable environment for their clients’ critical data and IT infrastructure.








